Netapprove starts every customer engagement with the same question: do you actually know what’s on your network? Within minutes of plugging into a SPAN port, you have a living inventory, a global flow map, and a per-device behavior fingerprint, with zero agents and zero downtime.

A real-time WebGL globe rendered from your conn.log. Cyan arcs are inbound, orange are outbound. Auto-rotates, filterable by direction, country, host, or peer. Click any arc to drill into the flow.

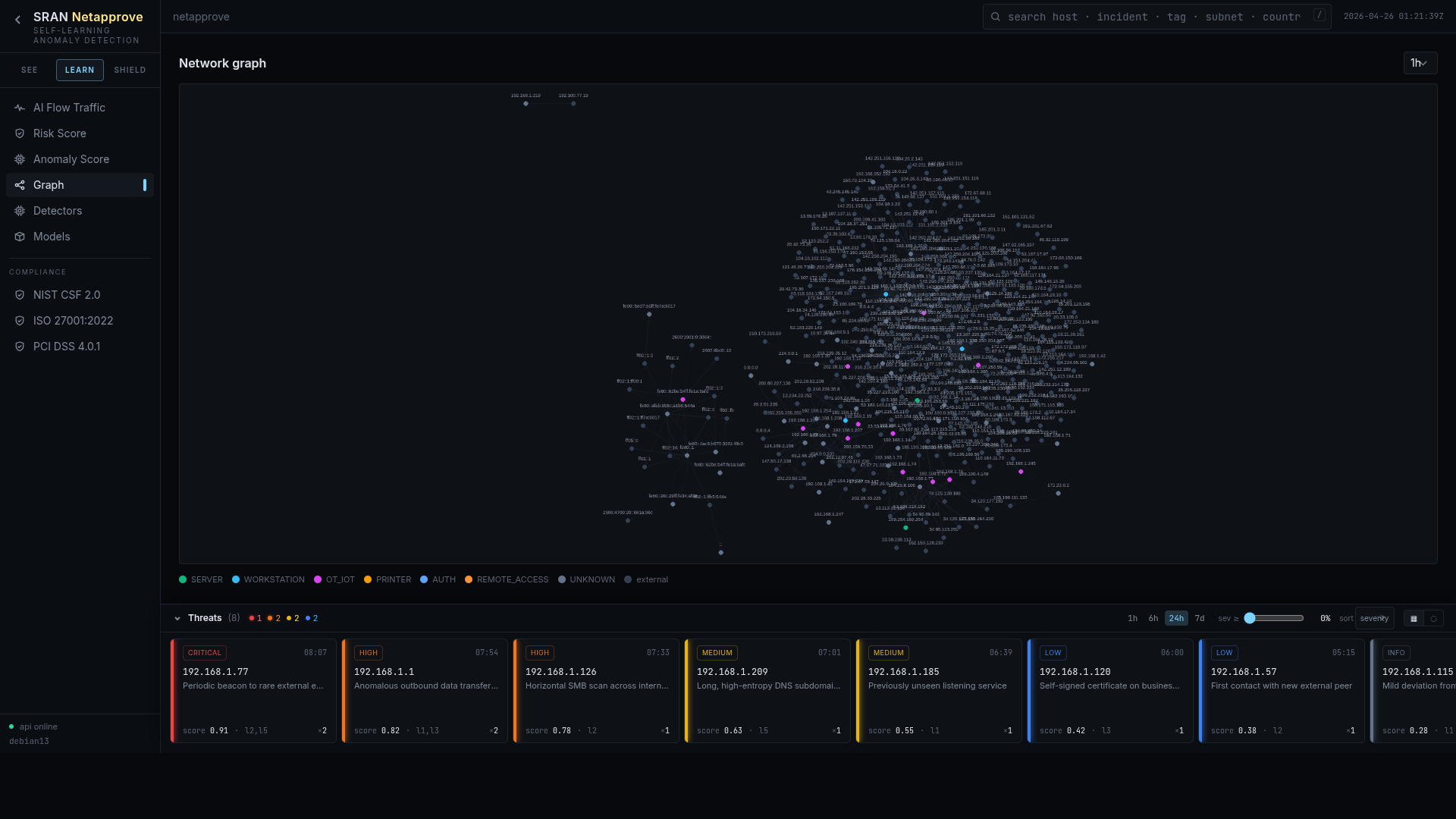
A force-directed map of every device and every conversation seen on the wire. Cluster colors map to subnet, to anomaly score, or to inferred role. The shape of your network, literally.
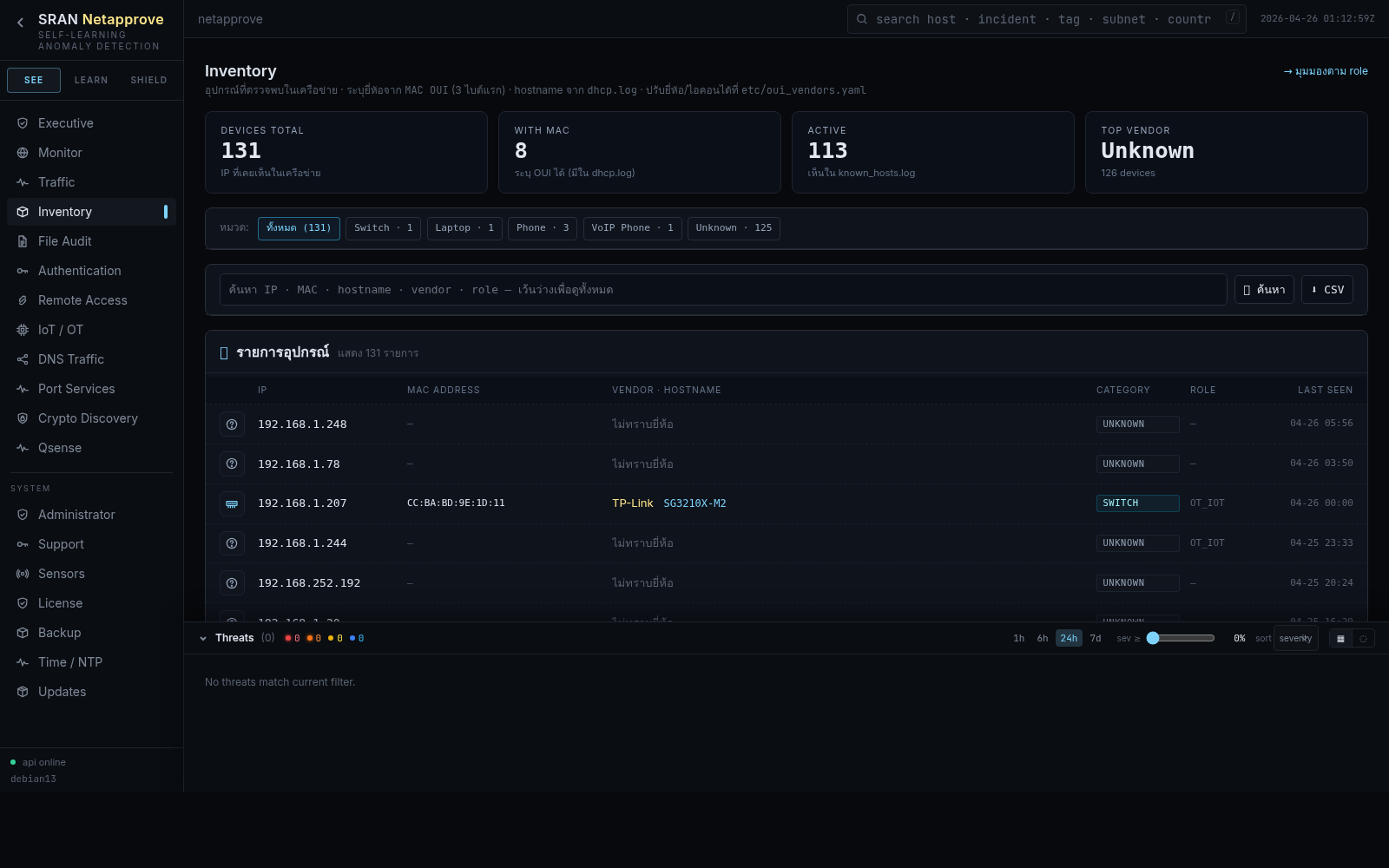
Every MAC, every IP, every hostname, reconciled across DHCP, NTLM, Kerberos, LDAP and RADIUS into one identity graph. The community-id correlation key threads each conversation across every log so an asset is never just "an IP".
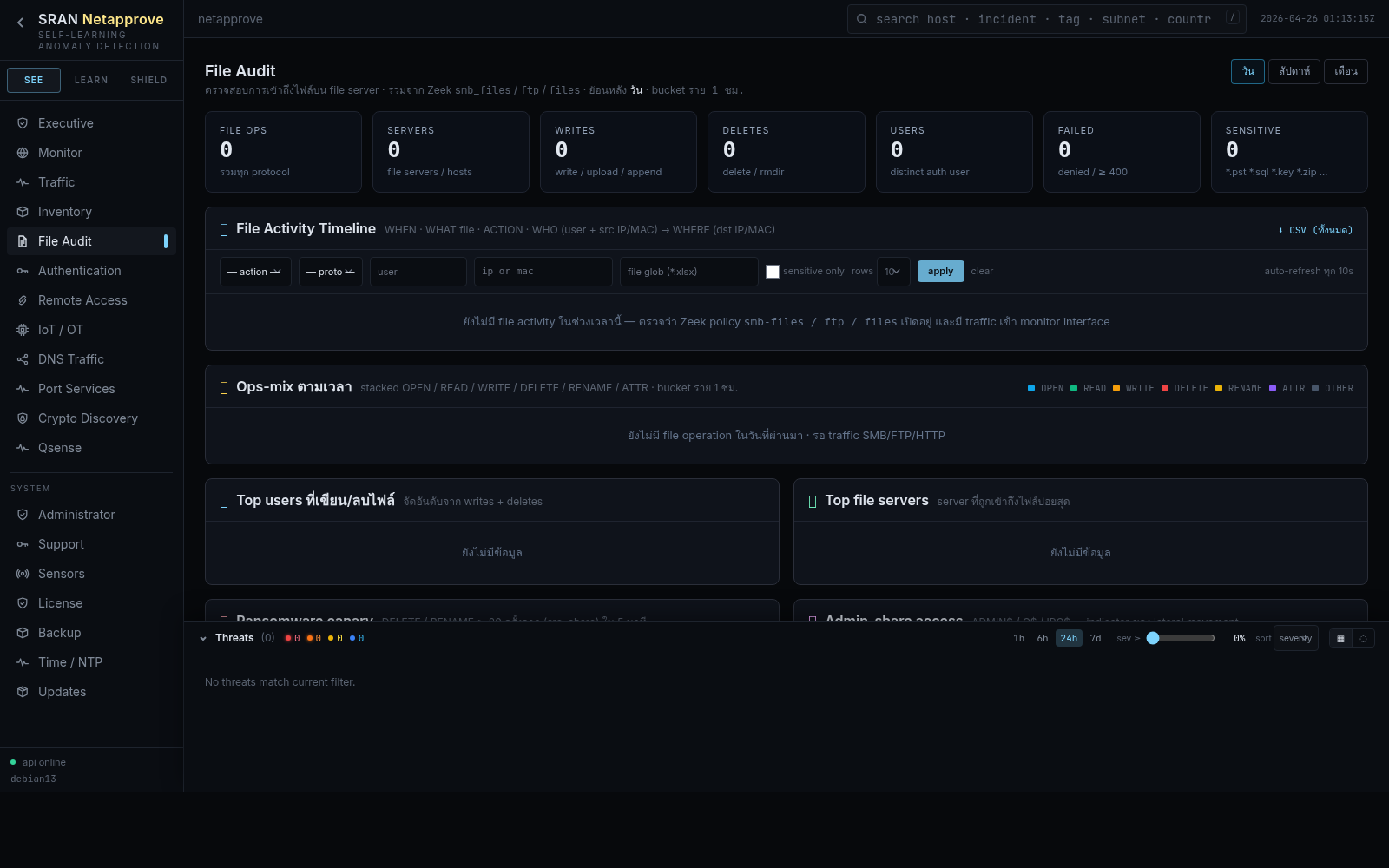
One unified timeline of every file moved on the network: SMB, FTP, HTTP, SMTP. Hash-matched, MIME-classified, and tied back to the host and account that initiated the transfer.
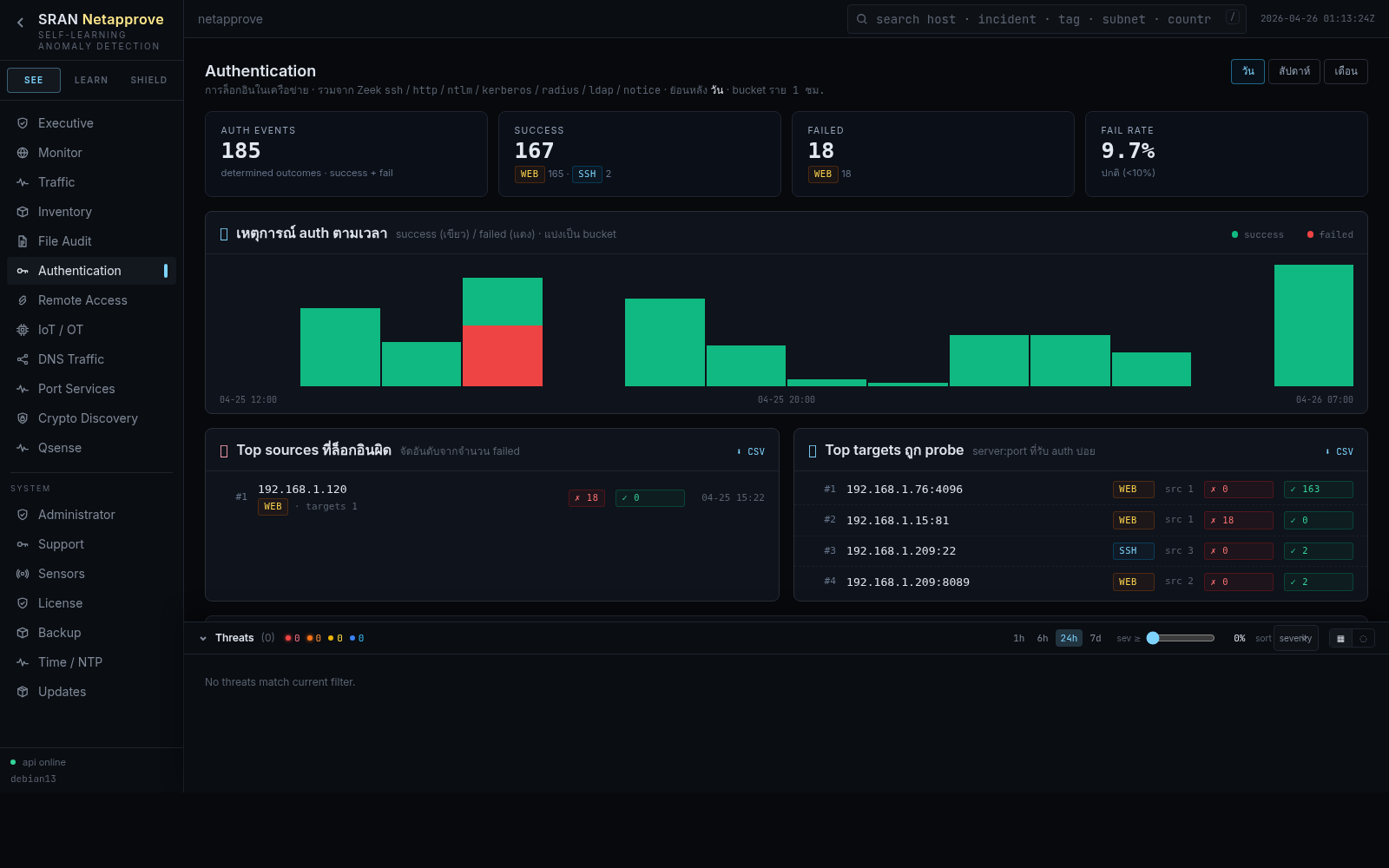
Every login attempt, SSH, web, NTLM, Kerberos, RADIUS, LDAP, in one queryable timeline. Brute force, credential stuffing, and impossible-travel detection ride on top.
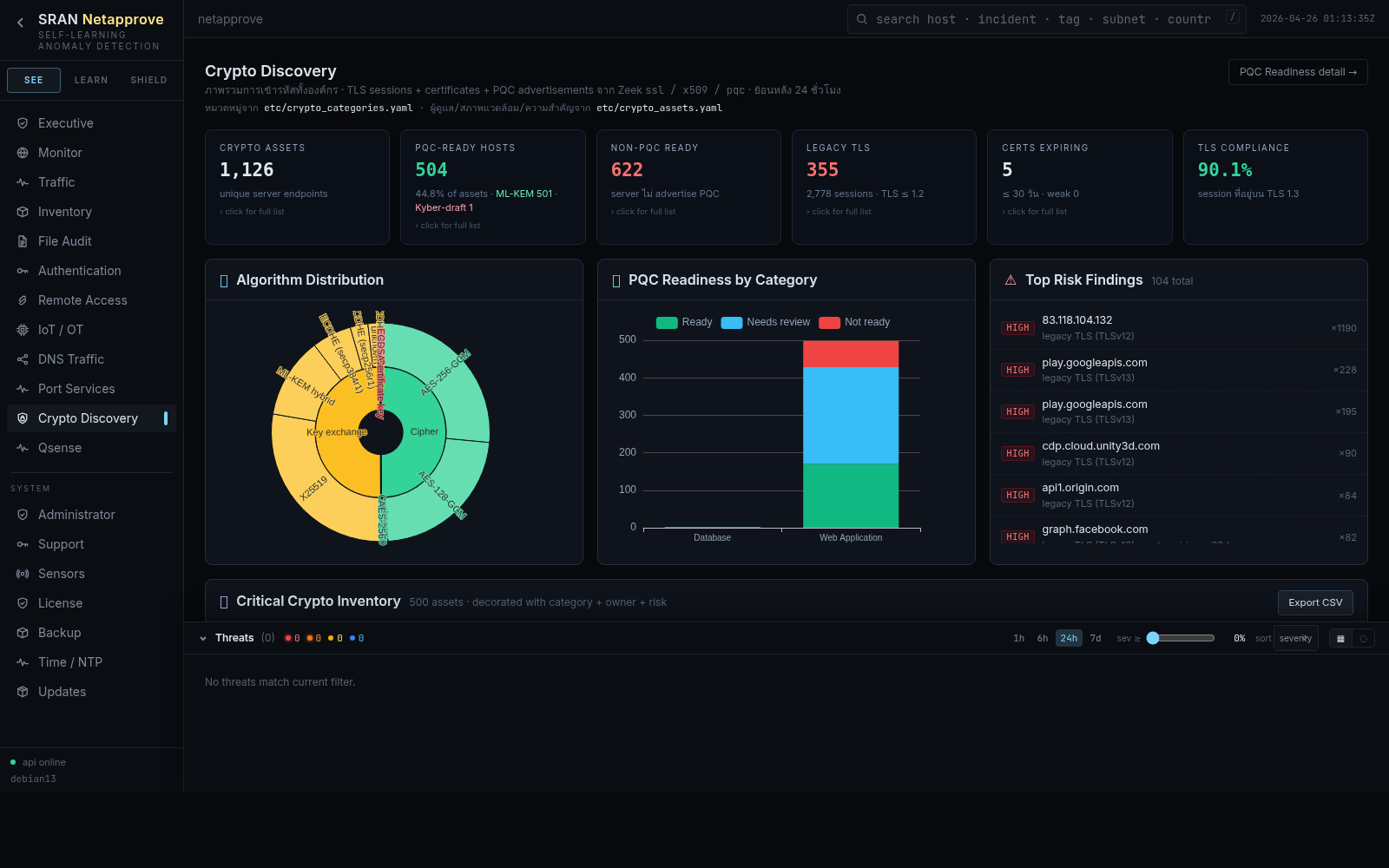
DNS Traffic surfaces tunneling, DGA, and beaconing. Crypto Discovery inventories every TLS suite, certificate, and SSH key, including a post-quantum readiness audit.
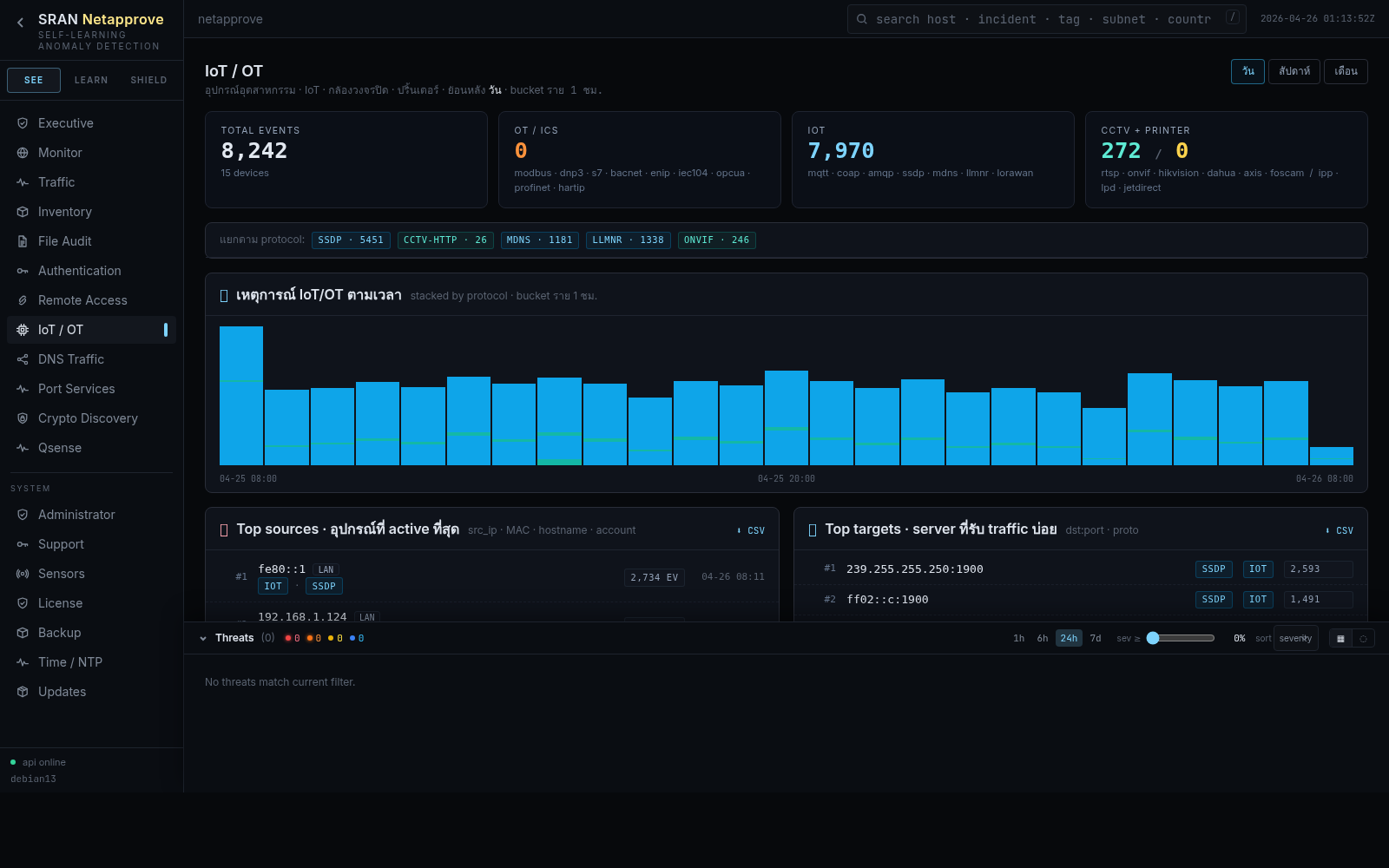
Printers, cameras, PLCs, SCADA. Anything you can’t install software on, Netapprove still discovers, fingerprints, and baselines from the wire alone.