COBIT 2019
ISACA Governance & Management of IT
IT governance, board oversight, control objectives mapped to detection & response evidence.
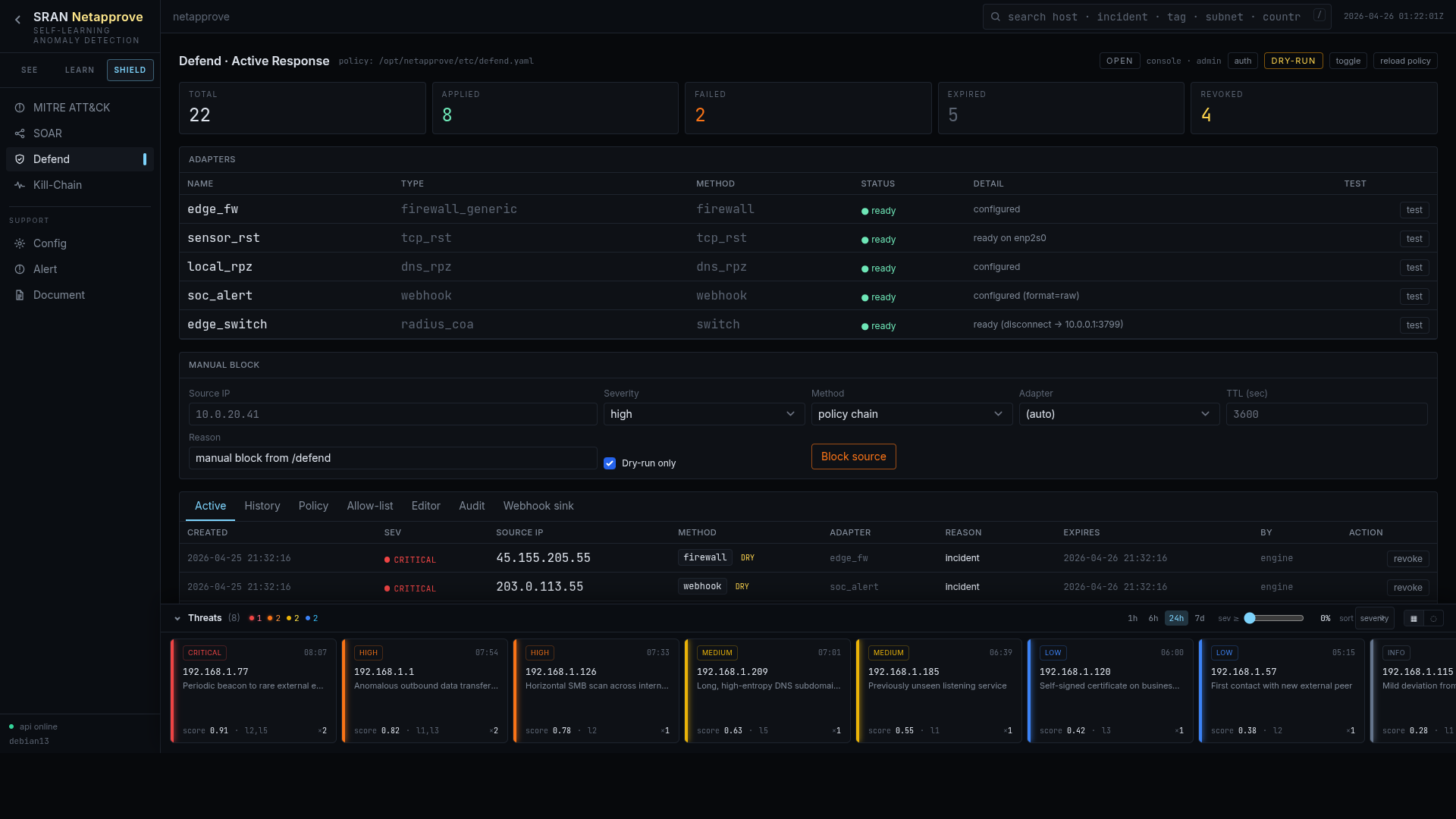
Netapprove was built around a simple belief: every confident detection should map to an executable action. We ship five active-response adapters out of the box, a full RBAC layer, and a dry-run-by-default safety policy, so the AI can act, and you stay in control.
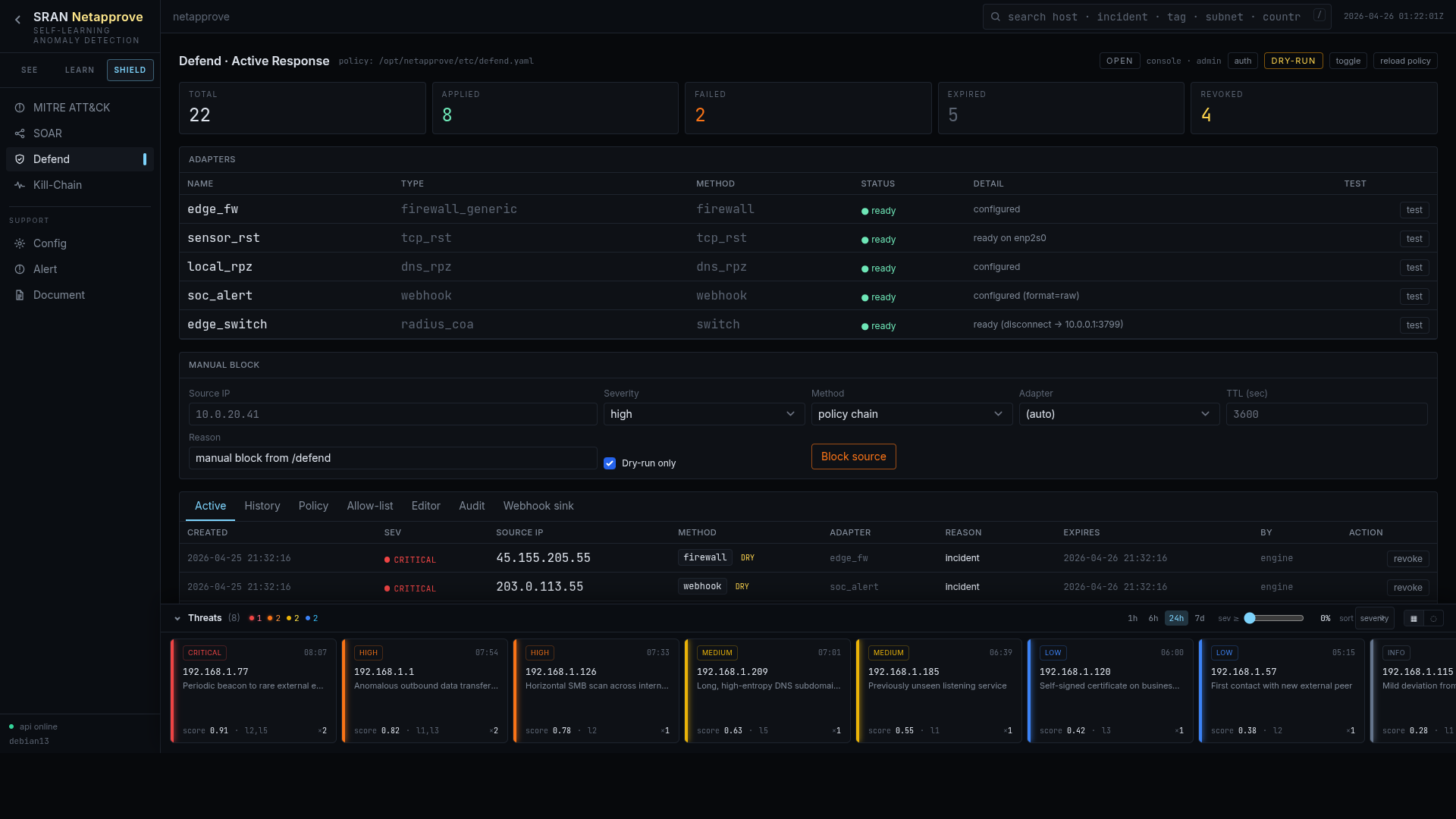
Each adapter speaks a real protocol, not a vendor-specific REST. That means Netapprove plugs into what you already own.
Pushes a deny rule to the perimeter firewall via firewalld / generic NETCONF / vendor REST. Auto-expires.
ACL or VLAN move on the access switch, quarantine an endpoint without unplugging the cable.
Posts a structured alert to your SOC channel (Slack / Teams / SIEM) with full context attached.
Runs a local response script, tcpdump capture, host triage, evidence preservation.
Change-of-Authorization on RADIUS / 802.1X. Boots a session, drops a port, swaps a VLAN, live.
Sinkhole a hostile FQDN on your resolver to neutralize C2 without touching endpoints.
Every new policy lands in dry-run mode. Netapprove logs what would have been blocked so you can audit a week of decisions before flipping a switch. Once you trust it, promote with one click.
The SOAR page lets you compose multi-step playbooks, "if a host beacons to a KEV-flagged peer for > 60s, capture pcap, sinkhole the FQDN, and quarantine the host via RADIUS CoA". Conditions, fan-out, and rollback are first-class.
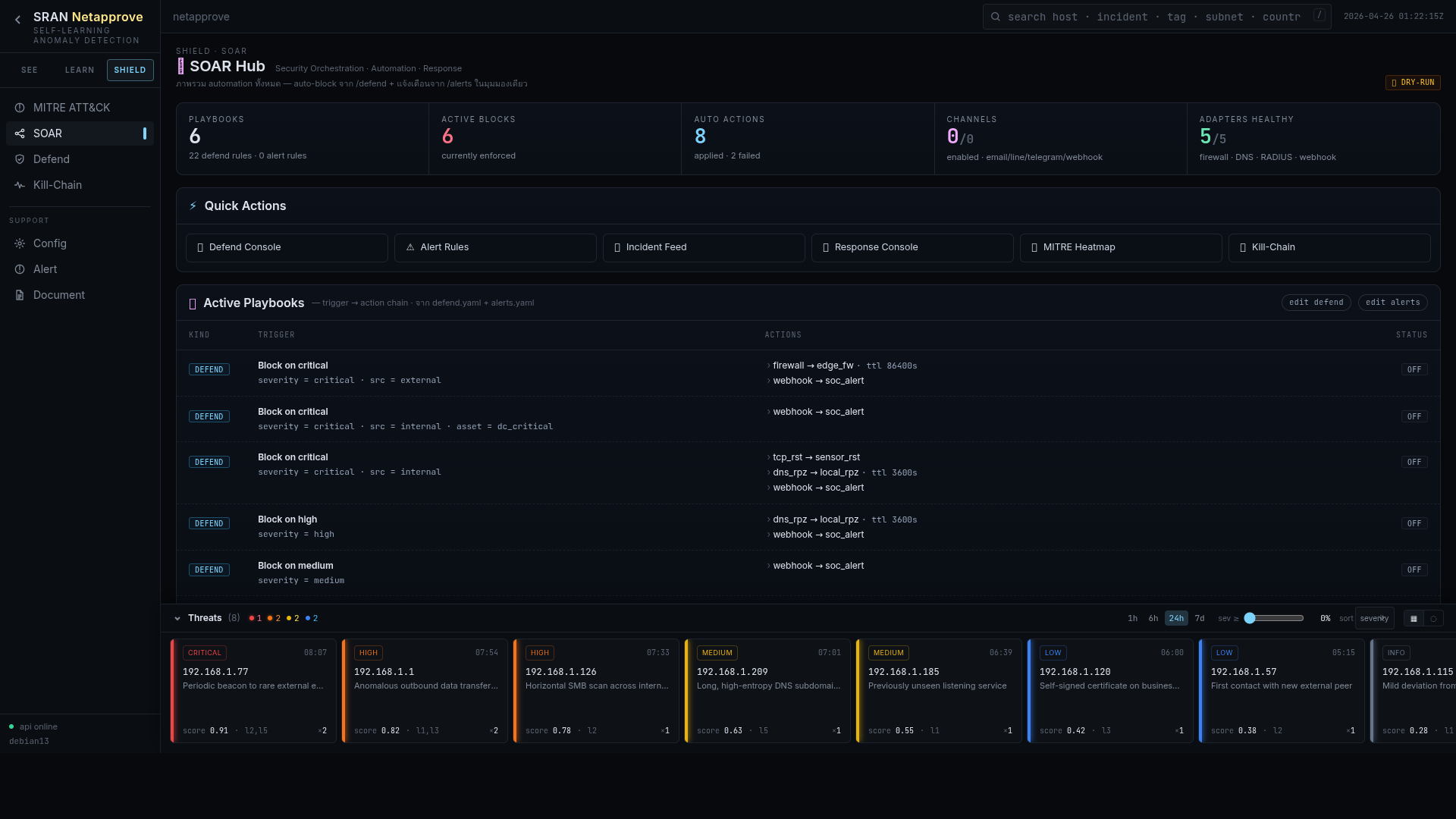
Every action, manual or automated, is signed, timestamped, and stored append-only. Three default roles (Administrator, Support, Read-Only) cover most tenants; custom roles are a checkbox grid away.

Netapprove maps every detection, every automated action, and every audit-log entry to internationally recognized control frameworks, used as a technical control library to fill in the engineering detail behind the regulator’s announcement, not to replace it.
ISACA Governance & Management of IT
IT governance, board oversight, control objectives mapped to detection & response evidence.
Information Security Management System
Annex A controls (A.5–A.8) evidenced via continuous monitoring, alerting, and signed audit log.
Information Security Risk Management
Live risk-score posture (A–F) feeds the ISO 27005 risk register with empirically observed exposure.
Privacy Information Management
Maps to PDPA / GDPR DPIA, surfaces processor and sub-processor traffic patterns for DPO review.
Business Continuity Management
RTO/RPO-relevant disruption detection; auto-evidence for BIA & recovery exercises.
Govern · Identify · Protect · Detect · Respond · Recover
Each Netapprove pillar (See / Learn / Shield) is tagged to the corresponding CSF function for one-to-one auditor mapping.
Security & Privacy Controls
SI-4 (system monitoring), AU-* (audit), IR-* (incident response) evidenced automatically.
Computer Security Incident Handling
LLM-generated triage narrative aligns to the Prepare · Detect · Contain · Eradicate · Recover lifecycle.
Technical Security Baseline (IG1–IG3)
Implementation Group evidence for CIS 13 (network monitoring) & CIS 17 (incident response).
Payment Card Industry Data Security
CDE segmentation evidence, Req. 10 logging, Req. 11 anomaly detection, Req. 12 incident response.
Supplier / Third-Party Security
Detects unsanctioned third-party traffic, shadow SaaS, and 4th-party data flows for supplier risk reviews.
The control library above is a starting point. Netapprove ships with a customizable mapping engine, auditors can tag any detection rule, baseline, or response action against your local regulator’s announcement (BoT, OIC, SEC, MAS, etc.) so that one signal produces evidence for multiple frameworks at once.